龙门客栈轶事——总店如何实现IPSec双链路备份连接分店?
(一)
龙门客栈是华夏武林中最有名的连锁客栈,服务热情价格公道,深受武林各路侠客的厚爱。客栈总店位于繁华的江南临安城,分店更是遍布华夏数十省,可谓家大业大,财富滚滚而来。
客栈创始人逍遥子武功卓绝、人品潇洒,数十年前就名满江湖。由于名气太大,每天都会收到江湖无名之辈的挑战书,不堪其扰之下,毅然退隐,创办龙门客栈,并立下规定:客人隐私大于一切,店小二对客人行踪严格保密。因此,各分店客人的入住记录,都会通过IPSec安全隧道的保护传至临安城总店机房,避免这些记录被宵小之徒窃取。
逍遥子决定采用性能强劲、稳定可靠的华三路由器作为总店/分店连接广域网的设备。为了保证IPSec传输可靠,临安城总店使用双链路接入Internet;而各省分店使用单链路接入Internet,以节省成本。
精心配置后,龙门客栈网络达到了如下效果:
1、总店与各分店之间的所有流量通过IPsec安全隧道进行传输。
2、总店主用链路正常时,所有流量通过主用链路进行传输。
3、当总店主用链路发生故障时,所有流量通过备用链路进行传输。
4、当总店主用链路恢复正常时,流量恢复从主用链路传输。
(二)
以上效果是如何实现的呢?下面我们来对龙门客栈的广域网组网进行模拟并分析:
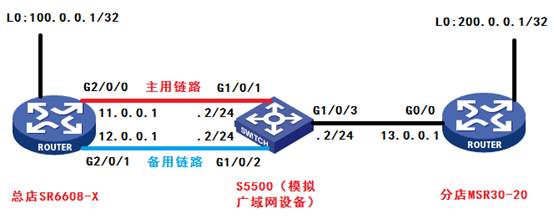
图1 组网模拟
上图中,我们使用SR6608-X路由器模拟总店路由器,使用MSR30-20路由器模拟某一分店路由器,使用S5500交换机模拟公网设备。
1、总店SR6608-X配置:
sysname SR6608-X
#
acl number 3000//NAT功能引用的ACL
rule 0 deny ip source 100.0.0.1 0 destination 200.0.0.1 0
rule 5 permit ip
acl number 3001//匹配Tunnel1的源/目的地址
rule 0 permit ip source 11.0.0.1 0 destination 13.0.0.1 0
acl number 3002//匹配Tunnel2的源/目的地址
rule 0 permit ip source 12.0.0.1 0 destination 13.0.0.1 0
#
Ike dpd 1
interval-time 1//触发DPD的时间间隔为1秒
time-out 3//DPD报文的重传时间间隔为2秒
#
ike peer 1
pre-shared-key h3c1
remote-address 13.0.0.1
local-address 11.0.0.1
dpd 1
#
ike peer 2
pre-shared-key h3c2
remote-address 13.0.0.1
local-address 11.0.0.1
dpd 1
#
ipsec transform-set 1
encapsulation-mode tunnel
transformesp
esp authentication-algorithm md5
esp encryption-algorithm 3des
#
ipsec transform-set 2
encapsulation-mode tunnel
transformesp
esp authentication-algorithm md5
esp encryption-algorithm 3des
#
ipsec policy 1 10 isakmp
securityacl 3001
ike-peer 1
transform-set 1
#
ipsec policy 2 10 isakmp
securityacl 3002
ike-peer 2
transform-set 2
#
interface LoopBack0//模拟总店业务网段
ip address 100.0.0.1 255.255.255.255
#
interfaceGigabitEthernet2/0/0
port link-mode route
nat outbound 3000
ip address 11.0.0.1 255.255.255.0
ipsec policy 1
#
interfaceGigabitEthernet2/0/1
port link-mode route
nat outbound 3000
ip address 12.0.0.1 255.255.255.0
ipsec policy 2
#
interfaceTunnel1
ip address 1.1.1.1 255.255.255.0
sourceGigabitEthernet2/0/0
destination 13.0.0.1
keepalive 3 3//keepalive报文发送周期为3秒,最大重传次数为3次,修改该值,可以调节链路收敛速度
#
interfaceTunnel2
ip address 2.2.2.1 255.255.255.0
sourceGigabitEthernet2/0/1
destination 13.0.0.1
keepalive 3 3
#
ip route-static 13.0.0.0 255.255.255.0 11.0.0.2 preference 10
ip route-static 13.0.0.0 255.255.255.0 12.0.0.2 preference 20
ip route-static 200.0.0.1 255.255.255.255 Tunnel1 preference 10
ip route-static 200.0.0.1 255.255.255.255 Tunnel2 preference 20
2、S5500配置:
sysnameS5500
#
vlan 1
#
vlan 2 to 4
#
interfaceVlan-interface2
ip address 11.0.0.2 255.255.255.0
#
interfaceVlan-interface3
ip address 12.0.0.2 255.255.255.0
#
interfaceVlan-interface4
ip address 13.0.0.2 255.255.255.0
#
interfaceGigabitEthernet1/0/1
port access vlan 2
#
interfaceGigabitEthernet1/0/2
port access vlan 3
#
interfaceGigabitEthernet1/0/3
port access vlan 4
3、分店MSR30-20配置:
sysname MSR30-20
#
acl number 3000//NAT功能引用的ACL
rule 0 deny ip source 200.0.0.1 0 destination 100.0.0.1 0
rule 5 permit ip
acl number 3001//匹配Tunnel1的源/目的地址
rule 0 permit ip source 13.0.0.1 0 destination 11.0.0.1 0
acl number 3002//匹配Tunnel2的源/目的地址
rule 0 permit ip source 13.0.0.1 0 destination 12.0.0.1 0
#
ikedpd 1
interval-time 1
time-out 3
#
ike peer 1
pre-shared-key h3c1
remote-address 11.0.0.1
local-address 13.0.0.1
dpd 1
#
ike peer 2
pre-shared-key h3c2
remote-address 12.0.0.1
local-address 13.0.0.1
dpd 1
#
ipsec transform-set 1
encapsulation-mode tunnel
transform esp
esp authentication-algorithm md5
esp encryption-algorithm 3des
#
ipsec transform-set 2
encapsulation-mode tunnel
transform esp
esp authentication-algorithm md5
esp encryption-algorithm 3des
#
ipsec policy 1 10 isakmp
securityacl 3001
ike-peer 1
transform-set 1
#
ipsec policy 1 20 isakmp
securityacl 3002
ike-peer 2
transform-set 2
#
interface LoopBack0//模拟分店业务网段
ip address 200.0.0.1 255.255.255.255
#
interfaceGigabitEthernet0/0
port link-mode route
nat outbound 3000
ip address 13.0.0.1 255.255.255.0
ipsec policy 1
#
interfaceTunnel1
ip address 1.1.1.2 255.255.255.0
sourceGigabitEthernet2/0/0
destination 11.0.0.1
keepalive 3 3
#
interfaceTunnel2
ip address 2.2.2.2 255.255.255.0
sourceGigabitEthernet2/0/0
destination 12.0.0.1
keepalive 3 3
#
ip route-static 11.0.0.0 255.255.255.0 13.0.0.2
ip route-static 12.0.0.0 255.255.255.0 13.0.0.2
ip route-static 100.0.0.1 255.255.255.255 Tunnel1 preference 10
ip route-static 100.0.0.1 255.255.255.255 Tunnel2 preference 20
(三)
以上配置完毕后,究竟能否达到总店IPSec双链路备份的效果?且看验证:1、在分店MSR30-20上,可见与总店的ikesa和ipsecsa成功建立:
<MSR30-20>display ike sa
total phase-1 SAs: 2
connection-id peer flag phase doi
----------------------------------------------------------------
49 12.0.0.1 RD|ST 1 IPSEC
51 11.0.0.1 RD|ST 1 IPSEC
38 12.0.0.1 RD|ST 2 IPSEC
52 11.0.0.1 RD|ST 2 IPSEC
<MSR30-20>display ipsec sa
===============================
Interface: GigabitEthernet0/0
path MTU: 1500
===============================
-----------------------------
IPsec policy name: "1"
sequence number: 10
acl version: ACL4
mode: isakmp
-----------------------------
PFS: N, DH group: none
tunnel:
local address: 13.0.0.1
remote address: 11.0.0.1
flow:
souraddr: 13.0.0.1/255.255.255.255 port: 0 protocol: IP
destaddr: 11.0.0.1/255.255.255.255 port: 0 protocol: IP
[inbound ESP SAs]
spi: 0xE20D88BC(3792537788)
transform: ESP-ENCRYPT-3DES ESP-AUTH-MD5
in use setting: Tunnel
connection id: 31
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1843140/1782
anti-replay detection: Enabled
anti-replay window size(counter based): 32
udp encapsulation used for nat traversal: N
[outbound ESP SAs]
spi: 0x85CFFBB3(2245000115)
transform: ESP-ENCRYPT-3DES ESP-AUTH-MD5
in use setting: Tunnel
connection id: 32
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1843140/1782
anti-replay detection: Enabled
anti-replay window size(counter based): 32
udp encapsulation used for nat traversal: N
===============================
Interface: GigabitEthernet0/0
path MTU: 1500
===============================
-----------------------------
IPsec policy name: "1"
sequence number: 20
acl version: ACL4
mode: isakmp
-----------------------------
PFS: N, DH group: none
tunnel:
local address: 13.0.0.1
remote address: 12.0.0.1
flow:
souraddr: 13.0.0.1/255.255.255.255 port: 0 protocol: IP
destaddr: 12.0.0.1/255.255.255.255 port: 0 protocol: IP
[inbound ESP SAs]
spi: 0x78CD223B(2026709563)
transform: ESP-ENCRYPT-3DES ESP-AUTH-MD5
in use setting: Tunnel
connection id: 25
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1843173/1535
anti-replay detection: Enabled
anti-replay window size(counter based): 32
udp encapsulation used for nat traversal: N
[outbound ESP SAs]
spi: 0x1B535923(458447139)
transform: ESP-ENCRYPT-3DES ESP-AUTH-MD5
in use setting: Tunnel
connection id: 26
sa duration (kilobytes/sec): 1843200/3600
sa remaining duration (kilobytes/sec): 1843145/1535
anti-replay detection: Enabled
anti-replay window size(counter based): 32
udp encapsulation used for nat traversal: N
2、将分店MSR30-20上的ike sa与ipsec sa清空,然后带源200.0.0.1长ping 总店SR6608-X的业务网段100.0.0.1:
<MSR30-20>ping -c 10000 -a 200.0.0.1 100.0.0.1
PING 100.0.0.1: 56 data bytes, press CTRL_C to break
Reply from 100.0.0.1: bytes=56 Sequence=0 ttl=255 time=1 ms
Reply from 100.0.0.1: bytes=56 Sequence=1 ttl=255 time=1 ms
Reply from 100.0.0.1: bytes=56 Sequence=2 ttl=255 time=1 ms
Reply from 100.0.0.1: bytes=56 Sequence=3 ttl=255 time=1 ms
Reply from 100.0.0.1: bytes=56 Sequence=4 ttl=255 time=1 ms
此时Tunnel 1处于UP状态,可见报文走主用链路Tunnel1转发:
<MSR30-20>display ip interface brief
*down: administratively down
(s): spoofing (l): loopback
Interface Physical Protocol IP Address Description
GE0/0 up up 13.0.0.1 --
Loop0 up up(s) 200.0.0.1 --
Tun1 up up 1.1.1.2 --
Tun2 down down 2.2.2.2 --
3、将总店SR6608-X主用链路断开后,观察报文能否能切换到备用链路:
Reply from 100.0.0.1: bytes=56 Sequence=47 ttl=255 time=1 ms
Reply from 100.0.0.1: bytes=56 Sequence=48 ttl=255 time=1 ms
Reply from 100.0.0.1: bytes=56 Sequence=49 ttl=255 time=1 ms
Request time out
Request time out
Request time out
Request time out
Reply from 100.0.0.1: bytes=56 Sequence=54 ttl=255 time=1 ms
Reply from 100.0.0.1: bytes=56 Sequence=55 ttl=255 time=1 ms
Reply from 100.0.0.1: bytes=56 Sequence=56 ttl=255 time=1 ms
答案是肯定的,在丢失数个报文后(大致10s左右),报文切换到备用链路上。这时再查看接口状态,发现Tunnel 1 down ,Tunnel 2 up,证明报文经由Tunnel 2进行转发:
<MSR30-20>displayip interface brief
*down: administratively down
(s): spoofing (l): loopback
Interface Physical Protocol IP Address Description
GE0/0 up up 13.0.0.1 --
Loop0 up up(s) 200.0.0.1 --
Tun1 down down 1.1.1.2 --
Tun2 up up 2.2.2.2 --
4、这时,我们再将SR6608-X主用链路恢复,观察报文能否切回主用链路:
Reply from 100.0.0.1: bytes=56 Sequence=84 ttl=255 time=1 ms
Reply from 100.0.0.1: bytes=56 Sequence=85 ttl=255 time=1 ms
Reply from 100.0.0.1: bytes=56 Sequence=86 ttl=255 time=1 ms
Request time out
Request time out
Request time out
Request time out
Request time out
Request time out
Request time out
Reply from 100.0.0.1: bytes=56 Sequence=94 ttl=255 time=1 ms
Reply from 100.0.0.1: bytes=56 Sequence=95 ttl=255 time=1 ms
Reply from 100.0.0.1: bytes=56 Sequence=96 ttl=255 time=1 ms
答案是肯定的。在丢失数个报文后,报文又会切回主用链路,时间也在10s左右。此时Tunnel1 UP、Tunnel2 DOWN :
<MSR30-20>displayip interface brief
*down: administratively down
(s): spoofing (l): loopback
Interface Physical Protocol IP Address Description
GE0/0 up up 13.0.0.1 --
Loop0 up up(s) 200.0.0.1 --
Tun1 up up 1.1.1.2 --
Tun2 down down 2.2.2.2 --
5、从总店带源100.0.0.1ping分店业务网段200.0.0.1,现象一致。
可见,总店IPSec双链路备份要求得到满足!

 新浪微博
新浪微博 腾讯微博
腾讯微博 豆瓣空间
豆瓣空间 搜狐微博
搜狐微博 QQ空间
QQ空间 腾讯朋友
腾讯朋友 网易微博
网易微博 百度搜藏
百度搜藏 告诉聊友
告诉聊友